Security Rule - The ePHI Guardian
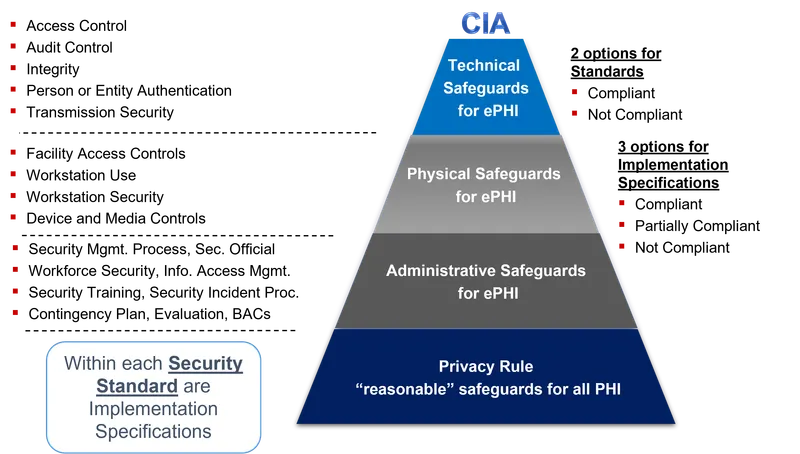
Mandates protection for all electronically protected health information (ePHI) created, received, used, or maintained by a covered entity. Focuses on confidentiality, integrity, and availability.
- Administrative Safeguards: Risk analysis, security officer designation, workforce training, contingency plan.
- Physical Safeguards: Facility access controls, workstation & device security, secure server rooms.
- Technical Safeguards: Unique user IDs, audit controls, encryption, transmission security.
⭐ The Rule is flexible, distinguishing between "required" and "addressable" implementation specifications based on entity-specific risk analysis.
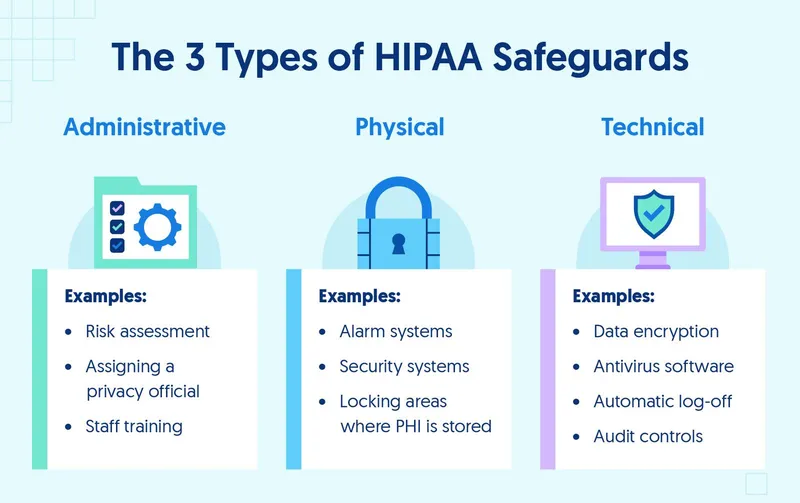
Administrative Safeguards - People & Policies
- Security Management Process:
- Conduct a formal Risk Analysis of potential threats to ePHI.
- Implement Risk Management measures to mitigate identified risks.
- Assigned Security Responsibility:
- Designate a specific Security Official to oversee all security policies.
- Workforce Security:
- Procedures for authorizing, supervising, and terminating workforce ePHI access.
- Information Access Management:
- Restrict access based on user roles ("minimum necessary" principle).
- Security Awareness & Training:
- Mandatory, periodic training for all staff on security policies (e.g., malware, passwords).
- Contingency & Incident Plan:
- Establish policies for data backup, disaster recovery, and incident response.
⭐ A covered entity must designate a specific Security Official responsible for developing and implementing all required security policies and procedures.
Physical Safeguards - Locks, Doors & Devices
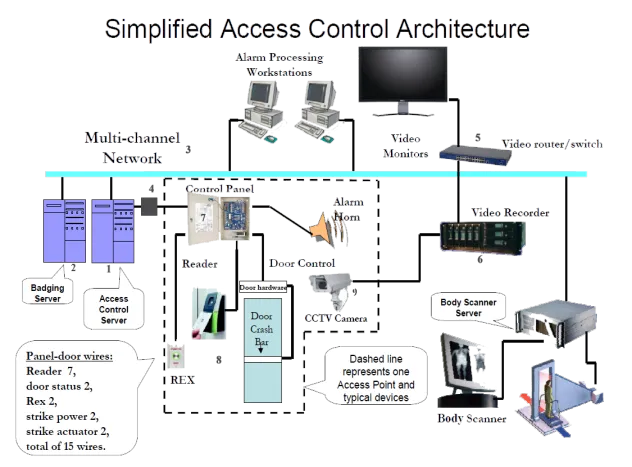
- Facility Access Controls: Secure physical access to areas containing ePHI. Implements locks, alarms, and key-card systems to restrict entry to authorized staff only.
- Workstation Security: Governs the physical environment of workstations accessing ePHI.
- Position screens away from public view.
- Implement automatic log-off policies after inactivity.
- Device & Media Controls: Policies for handling hardware and media.
- Disposal: Render ePHI unrecoverable via pulverizing, melting, or degaussing.
- Re-Use: Securely wipe data before re-using devices.
⭐ Improper disposal of devices containing ePHI is a common HIPAA violation. Policies must ensure data is permanently destroyed (e.g., degaussing, physical destruction), not just deleted.
Technical Safeguards - The Digital Fortress
- Access Control: Limiting access to authorized personnel.
- Unique User Identification: Assigning a unique name/number for tracking.
- Emergency Access Procedure: Ensuring data availability during crises.
- Automatic Logoff: Terminating sessions after a period of inactivity.
- Audit Controls: Hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI.
- Integrity: Policies and procedures to protect ePHI from improper alteration or destruction.
- Transmission Security: Guarding against unauthorized access to ePHI being transmitted over a network.
- Encryption is the primary method.
⭐ High-Yield Fact: Encryption is an "addressable" safeguard, but if not used, an equivalent measure must be implemented. It renders ePHI unusable, unreadable, or indecipherable to unauthorized individuals.
High‑Yield Points - ⚡ Biggest Takeaways
- The Security Rule applies exclusively to electronic protected health information (e-PHI).
- It mandates three core safeguards: Administrative, Physical, and Technical.
- Administrative safeguards include performing a risk analysis and designating a security official.
- Physical safeguards focus on controlling access to facilities and securing workstations.
- Technical safeguards require access controls (unique user IDs), audit logs, and encryption of e-PHI during transmission.
Unlock the full lesson and continue reading
Signup to continue reading this lesson and unlimited access questions, flashcards, AI notes, and more

